Nextelco:ASA VPN DHCPrelay
DHCP through VPN
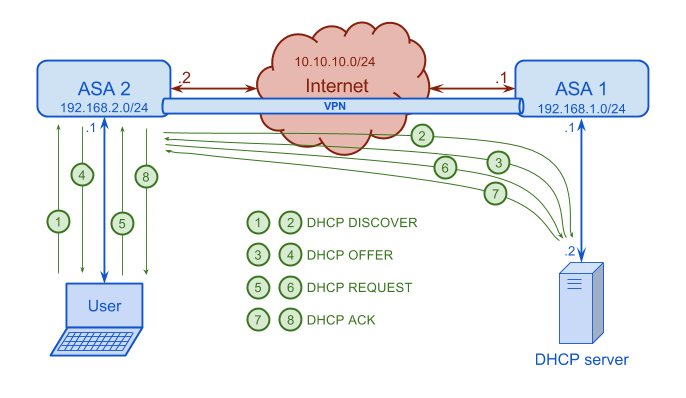
Is time to set up something really useful. In our general schema we have some site to site VPNs between ASA devices sitting on Africa and Norway. In order to have a centralized DHCP server it is necessary to configure ASAs in order to provide DHCP requests and replies through the VPN. In the following Figure we can see the configuration details.
In order to set the DHCP configuration, first we need to set up the initial configuration and the VPN between these two ASAs. In order to set up the initial configuration refer to the following configuration steps.
At this point, it is necessary to understand how DHCP and specially DHCP relay works in order to know how to set up everything. So, these are the necessary steps:
-
The client, user machine, broadcasts a DHCP DISCOVER packet.
- IP source: 0.0.0.0
- IP destination: 255.255.255.255
- Port source: 68
- Port destination: 67
- Relay agent IP address: 0.0.0.0
-
ASA2 takes the packet and based on its DHCP relay configuration it sends the DHCP DISCOVER packet directly to the DCHP server.
- IP source: 10.10.10.2
- IP destination: 192.168.1.2
- Port source: 67
- Port destination: 67
- Relay agent IP address: 192.168.2.1
-
The DCHP server takes the DHCP DISCOVER packet and it replies with a DHCP OFFER. It sends the offer to the RELAY AGENT (ASA2).
- IP source: 192.168.1.2
- IP destination: 192.168.2.1
- Port source: 67
- Port destination: 67
- Relay agent IP address: 192.168.2.1
- Your IP address: 192.168.2.2
-
ASA2 takes the DHCP OFFER and it sends to the client.
- IP source: 192.168.2.1
- IP destination: 192.168.2.2
- Port source: 67
- Port destination: 68
- Relay agent IP address: 192.168.2.1
- Your IP address: 192.168.2.2
-
The client starts with the DCHP REQUEST.
- IP source: 0.0.0.0
- IP destination: 255.255.255.255
- Port source: 68
- Port destination: 67
- Relay agent IP address: 0.0.0.0
- DHCP server: 192.168.1.2
- Requested IP address: 192.168.2.2
-
ASA2 takes the REQUEST and it forwards to the DHCP server.
- IP source: 10.10.10.2
- IP destination: 192.168.1.2
- Port source: 67
- Port destination: 67
- Relay agent IP address: 192.168.2.1
- DHCP server: 192.168.1.2
- Requested IP address: 192.168.2.2
-
The DHCP server takes the REQUEST and replies with a DHCP ACK.
- IP source: 192.168.1.2
- IP destination: 192.168.2.1
- Port source: 67
- Port destination: 67
- Relay agent IP address: 192.168.2.1
- DHCP server: 192.168.1.2
- Your IP address: 192.168.2.2
-
Last step. ASA2 takes the ACK and it forwards to the client.
- IP source: 192.168.2.1
- IP destination: 192.168.2.2
- Port source: 67
- Port destination: 68
- Relay agent IP address: 192.168.2.1
- DHCP server: 192.168.1.2
- Your IP address: 192.168.2.2
In order to allow DHCP traffic through the VPN it is necessary to set up both, ASA1 and ASA2. These are the configuration files of both of them.
ASA1
: Saved : ASA Version 8.2(5) ! hostname ASA1 enable password 8Ry2YjIyt7RRXU24 encrypted passwd 2KFQnbNIdI.2KYOU encrypted names ! interface Ethernet0/0 switchport access vlan 2 ! interface Ethernet0/1 ! interface Ethernet0/2 shutdown ! interface Ethernet0/3 shutdown ! interface Ethernet0/4 shutdown ! interface Ethernet0/5 shutdown ! interface Ethernet0/6 shutdown ! interface Ethernet0/7 shutdown ! interface Vlan1 nameif inside security-level 100 ip address 192.168.1.1 255.255.255.0 ! interface Vlan2 nameif outside security-level 0 ip address 10.10.10.1 255.255.255.0 ! ftp mode passive object-group network DHCP_SERVER description DHCP server IP address. network-object host 192.168.1.2 object-group network ASA1_INSIDE_NET description ASA1 inside network address. network-object 192.168.1.0 255.255.255.0 object-group network ASA2_INSIDE_NET description ASA2 inside network address. network-object 192.168.2.0 255.255.255.0 object-group network ASA2_OUTSIDE_IP description ASA2 outside interface IP address. network-object host 10.10.10.2 access-list CRYPTO_LAN_TO_LAN extended permit ip object-group DHCP_SERVER object-group ASA2_OUTSIDE_IP access-list CRYPTO_LAN_TO_LAN extended permit ip object-group ASA1_INSIDE_NET object-group ASA2_INSIDE_NET access-list INSIDE_NAT_OUTSIDE extended permit ip object-group ASA1_INSIDE_NET any access-list CRYPTO_NO_NAT extended permit ip object-group DHCP_SERVER object-group ASA2_OUTSIDE_IP access-list CRYPTO_NO_NAT extended permit ip object-group ASA1_INSIDE_NET object-group ASA2_INSIDE_NET pager lines 24 mtu inside 1500 mtu outside 1500 icmp unreachable rate-limit 1 burst-size 1 no asdm history enable arp timeout 14400 global (outside) 1 interface nat (inside) 0 access-list CRYPTO_NO_NAT nat (inside) 1 access-list INSIDE_NAT_OUTSIDE route outside 192.168.2.0 255.255.255.0 10.10.10.2 1 timeout xlate 3:00:00 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:01:00 timeout floating-conn 0:00:00 dynamic-access-policy-record DfltAccessPolicy aaa authentication ssh console LOCAL no snmp-server location no snmp-server contact snmp-server enable traps snmp authentication linkup linkdown coldstart crypto ipsec transform-set ESP-3DES-SHA esp-des esp-sha-hmac crypto ipsec security-association lifetime seconds 28800 crypto ipsec security-association lifetime kilobytes 4608000 crypto map MAP_CRYPTO_LAN_TO_LAN 1 match address CRYPTO_LAN_TO_LAN crypto map MAP_CRYPTO_LAN_TO_LAN 1 set pfs group1 crypto map MAP_CRYPTO_LAN_TO_LAN 1 set peer 10.10.10.2 crypto map MAP_CRYPTO_LAN_TO_LAN 1 set transform-set ESP-3DES-SHA crypto map MAP_CRYPTO_LAN_TO_LAN interface outside crypto isakmp enable outside crypto isakmp policy 10 authentication pre-share encryption 3des hash sha group 2 lifetime 86400 crypto isakmp policy 65535 authentication pre-share encryption 3des hash sha group 2 lifetime 86400 telnet timeout 5 ssh 192.168.1.0 255.255.255.0 inside ssh timeout 5 console timeout 0 threat-detection basic-threat threat-detection statistics access-list no threat-detection statistics tcp-intercept username basicinternet password UVFcpWay5BJPKJFl encrypted privilege 15 tunnel-group 10.10.10.2 type ipsec-l2l tunnel-group 10.10.10.2 ipsec-attributes pre-shared-key ***** ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map parameters message-length maximum client auto message-length maximum 512 policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect ip-options inspect netbios inspect rsh inspect rtsp inspect skinny inspect esmtp inspect sqlnet inspect sunrpc inspect tftp inspect sip inspect xdmcp inspect icmp ! service-policy global_policy global prompt hostname context no call-home reporting anonymous call-home profile CiscoTAC-1 no active destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService destination address email callhome@cisco.com destination transport-method http subscribe-to-alert-group diagnostic subscribe-to-alert-group environment subscribe-to-alert-group inventory periodic monthly subscribe-to-alert-group configuration periodic monthly subscribe-to-alert-group telemetry periodic daily Cryptochecksum:fac7c4dec8271bb4b049cfd63b0e2a71 : end
ASA2
: Saved : ASA Version 8.0(5) ! hostname ASA2 enable password 8Ry2YjIyt7RRXU24 encrypted passwd 2KFQnbNIdI.2KYOU encrypted names ! interface Vlan1 nameif inside security-level 100 ip address 192.168.2.1 255.255.255.0 ! interface Vlan2 nameif outside security-level 0 ip address 10.10.10.2 255.255.255.0 ! interface Ethernet0/0 switchport access vlan 2 ! interface Ethernet0/1 ! interface Ethernet0/2 shutdown ! interface Ethernet0/3 shutdown ! interface Ethernet0/4 shutdown ! interface Ethernet0/5 shutdown ! interface Ethernet0/6 shutdown ! interface Ethernet0/7 shutdown ! boot system disk0:/asa805-k8.bin ftp mode passive object-group network DHCP_SERVER description DHCP server IP address. network-object host 192.168.1.2 object-group network ASA1_INSIDE_NET description ASA1 inside network address. network-object 192.168.1.0 255.255.255.0 object-group network ASA2_INSIDE_NET description ASA2 inside network address. network-object 192.168.2.0 255.255.255.0 object-group network ASA2_OUTSIDE_IP description ASA2 outside interface IP address. network-object host 10.10.10.2 access-list INSIDE_NAT_OUTSIDE extended permit ip object-group ASA2_INSIDE_NET any access-list CRYPTO_NO_NAT extended permit ip object-group ASA2_OUTSIDE_IP object-group DHCP_SERVER access-list CRYPTO_NO_NAT extended permit ip object-group ASA2_INSIDE_NET object-group ASA1_INSIDE_NET access-list CRYPTO_LAN_TO_LAN extended permit ip object-group ASA2_OUTSIDE_IP object-group DHCP_SERVER access-list CRYPTO_LAN_TO_LAN extended permit ip object-group ASA2_INSIDE_NET object-group ASA1_INSIDE_NET pager lines 24 mtu inside 1500 mtu outside 1500 icmp unreachable rate-limit 1 burst-size 1 no asdm history enable arp timeout 14400 global (outside) 1 interface nat (inside) 0 access-list CRYPTO_NO_NAT nat (inside) 1 access-list INSIDE_NAT_OUTSIDE route outside 192.168.1.0 255.255.255.0 10.10.10.1 1 timeout xlate 3:00:00 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:01:00 dynamic-access-policy-record DfltAccessPolicy aaa authentication ssh console LOCAL no snmp-server location no snmp-server contact snmp-server enable traps snmp authentication linkup linkdown coldstart crypto ipsec transform-set ESP-3DES-SHA esp-des esp-sha-hmac crypto ipsec security-association lifetime seconds 28800 crypto ipsec security-association lifetime kilobytes 4608000 crypto map MAP_CRYPTO_LAN_TO_LAN 1 match address CRYPTO_LAN_TO_LAN crypto map MAP_CRYPTO_LAN_TO_LAN 1 set pfs group1 crypto map MAP_CRYPTO_LAN_TO_LAN 1 set peer 10.10.10.1 crypto map MAP_CRYPTO_LAN_TO_LAN 1 set transform-set ESP-3DES-SHA crypto map MAP_CRYPTO_LAN_TO_LAN interface outside crypto isakmp enable outside crypto isakmp policy 10 authentication pre-share encryption 3des hash sha group 2 lifetime 86400 crypto isakmp policy 65535 authentication pre-share encryption 3des hash sha group 2 lifetime 86400 no crypto isakmp nat-traversal telnet timeout 5 ssh 192.168.2.0 255.255.255.0 inside ssh timeout 5 console timeout 0 dhcprelay server 192.168.1.2 outside dhcprelay enable inside dhcprelay timeout 60 threat-detection basic-threat threat-detection statistics access-list no threat-detection statistics tcp-intercept username basicinternet password UVFcpWay5BJPKJFl encrypted privilege 15 tunnel-group 10.10.10.1 type ipsec-l2l tunnel-group 10.10.10.1 ipsec-attributes pre-shared-key * ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map parameters message-length maximum 512 policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect netbios inspect rsh inspect rtsp inspect skinny inspect esmtp inspect sqlnet inspect sunrpc inspect tftp inspect sip inspect xdmcp inspect icmp ! service-policy global_policy global prompt hostname context Cryptochecksum:d1cc3c831f3b6d6cf2c4df715e57b9b7 : end
Return to Phase 1 page.