Difference between revisions of "SCOTT:Overview of Responsibilities for UiO"
From its-wiki.no
(→UiO Related Building Blocks) |
(→UiO Related Building Blocks) |
||
| Line 32: | Line 32: | ||
[[SCOTT:HW supported security mechanisms|SCOTT-HW supported security mechanisms]] | [[SCOTT:HW supported security mechanisms|SCOTT-HW supported security mechanisms]] | ||
| + | |||
| + | [[SCOTT:SCOTT Security Library|SCOTT-SCOTT Security Library]] | ||
| + | |||
| + | |||
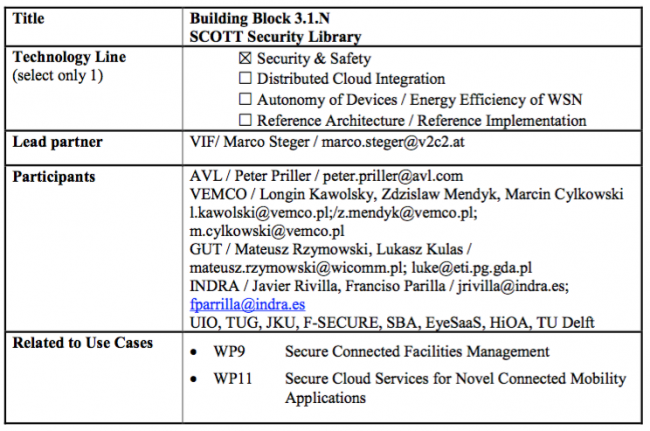
==SCOTT Security Library== | ==SCOTT Security Library== | ||
Revision as of 09:34, 7 June 2017
| Overview of Responsibilities for UiO | ||||||
|---|---|---|---|---|---|---|
|
Contents
- 1 Deliverables
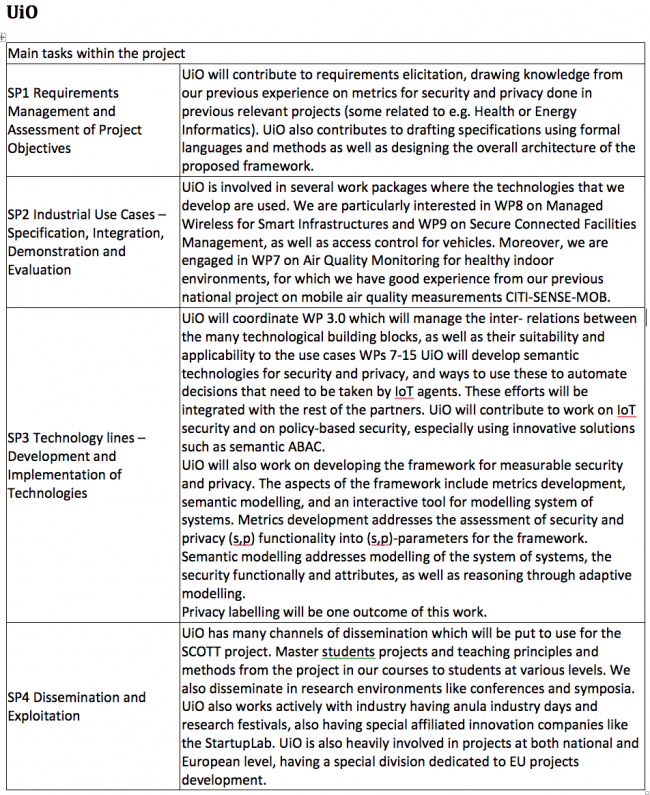
- 2 UiO Main tasks within the project
- 3 UiO involvement in Work Packages
- 4 UiO Related Building Blocks
- 4.1 SCOTT Security Library
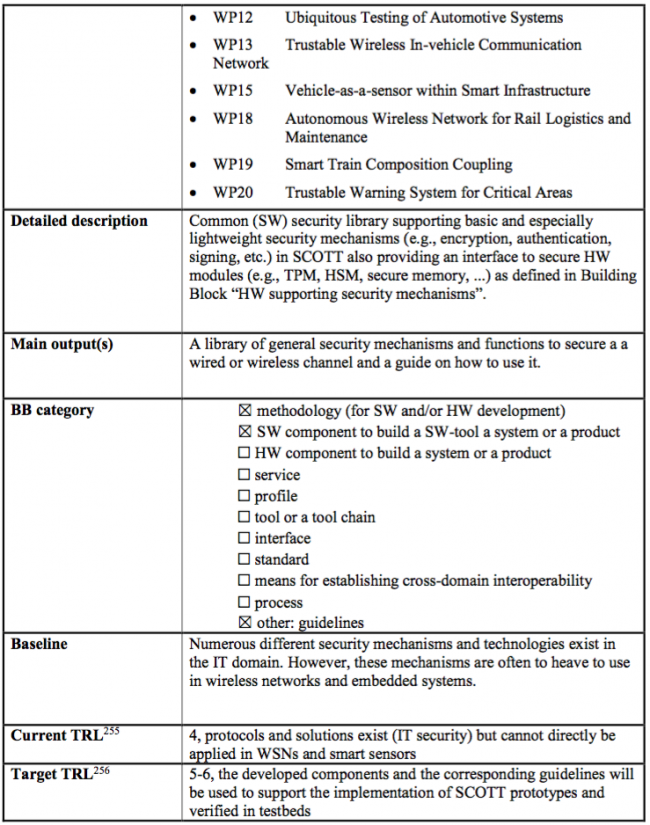
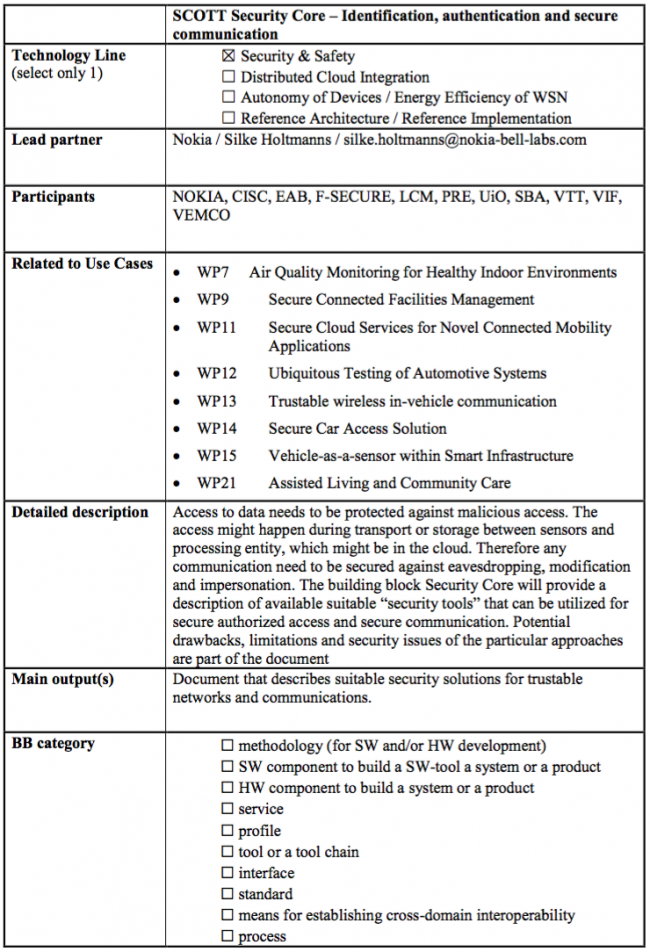
- 4.2 SCOTT Security Core – Identification, authentication and secure communication
- 4.3 Trust Anchor and Trust Indicator for ES and smart sensors
- 4.4 Remote Configuration of Infrastructure
- 4.5 Mobile Edge Computing
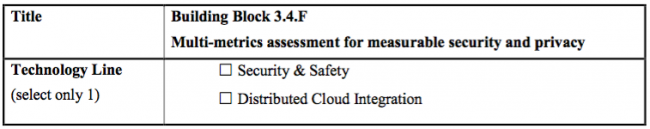
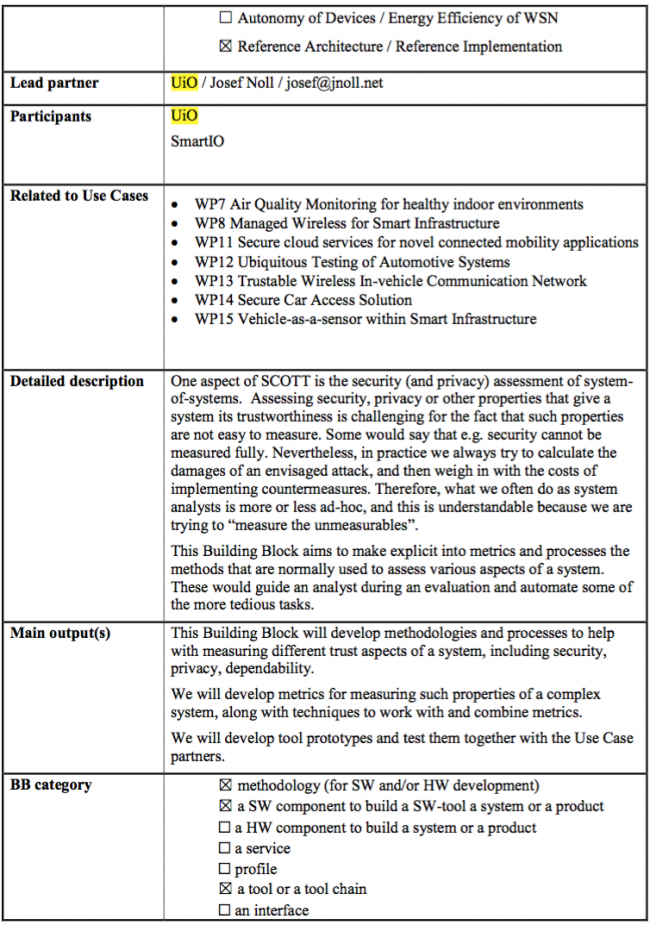
- 4.6 Multi-metrics assessment for measurable security and privacy
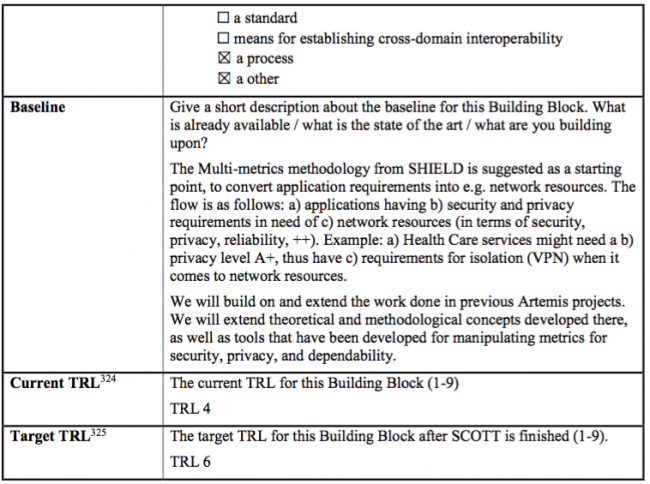
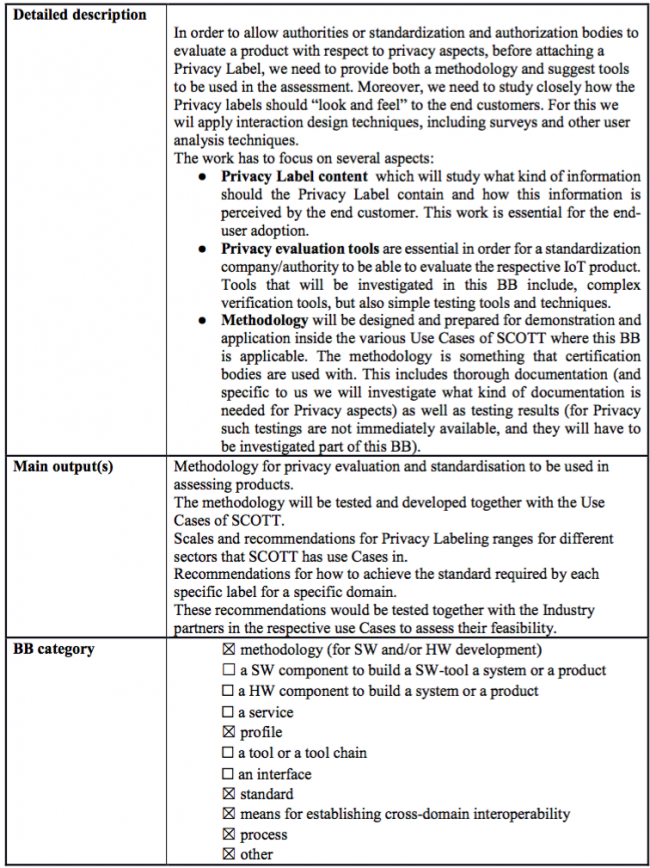
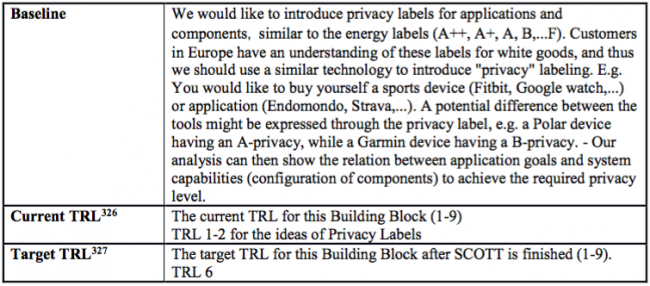
- 4.7 Privacy labels (A-F)
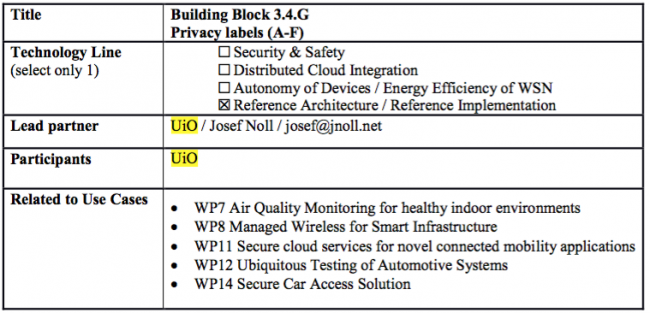
Deliverables
Start: 1May2017, thus M04 = 1Sep2017, M07 = 1Dec2017, ...
- Deliverables for each Lead partner is sorted based on its Due month
| Title | Due month | Lead partner | Editor | Dissemination level | |
|---|---|---|---|---|---|
| D22.1 | Assessment of technology | M12 | UiO | Toktam Ramezanifarkhani | Public |
| D22.3 | Trust technologies advances | M24 | UiO | Maunya Doroudi Moghadam | Public |
| D30.3 | Documentation of open innovation activities | M36 | UiO | Maunya Doroudi Moghadam | Confidential |
UiO Main tasks within the project
WT6 Summary of project effort in person-months for UiO
UiO involvement in Work Packages
Overview of UiO involvement in Work Packages in details
UiO Related Building Blocks
SCOTT-Semantic Attribute Based Access Control (S-ABAC)
SCOTT-HW supported security mechanisms
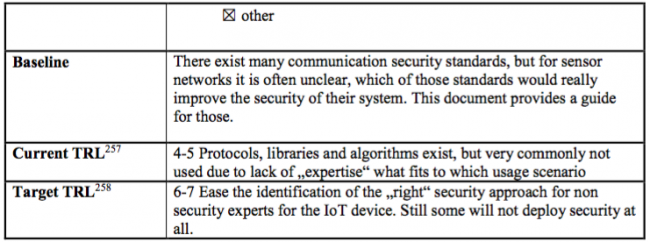
SCOTT Security Library
SCOTT Security Core – Identification, authentication and secure communication
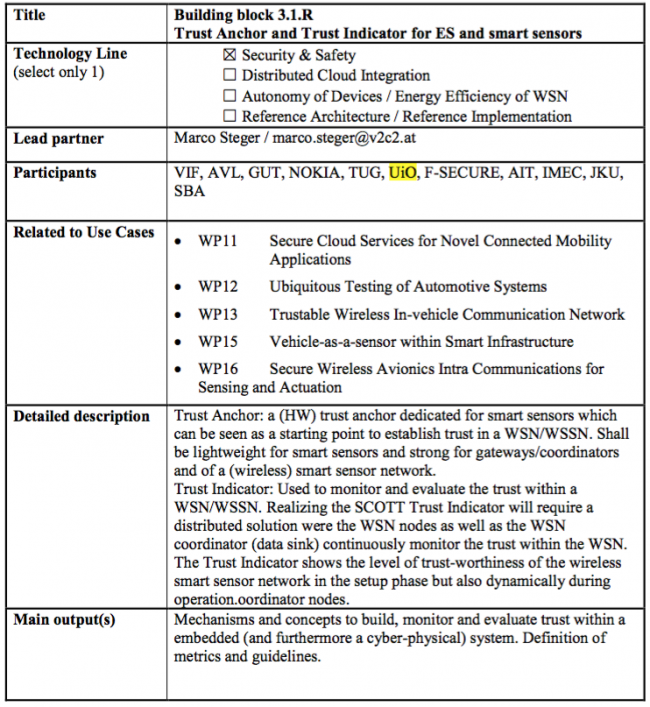
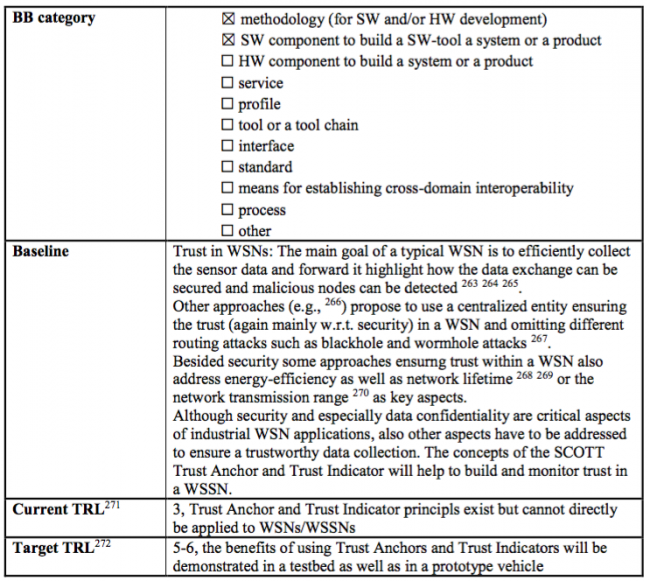
Trust Anchor and Trust Indicator for ES and smart sensors
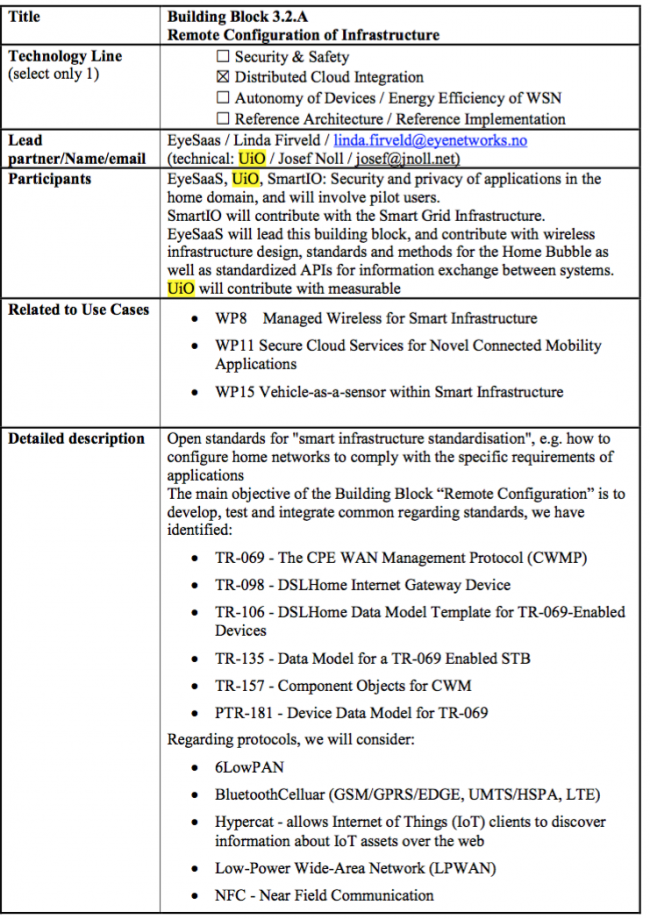
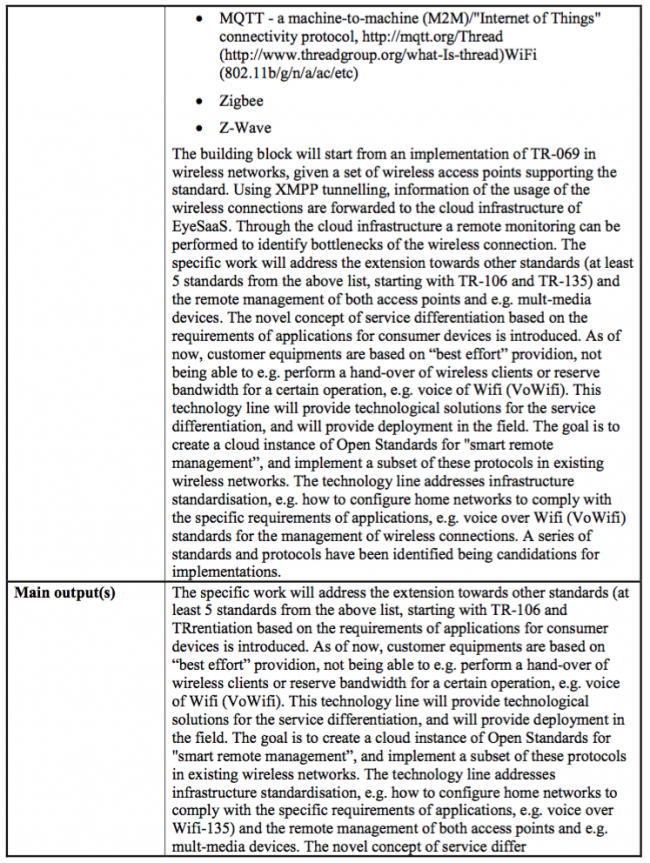
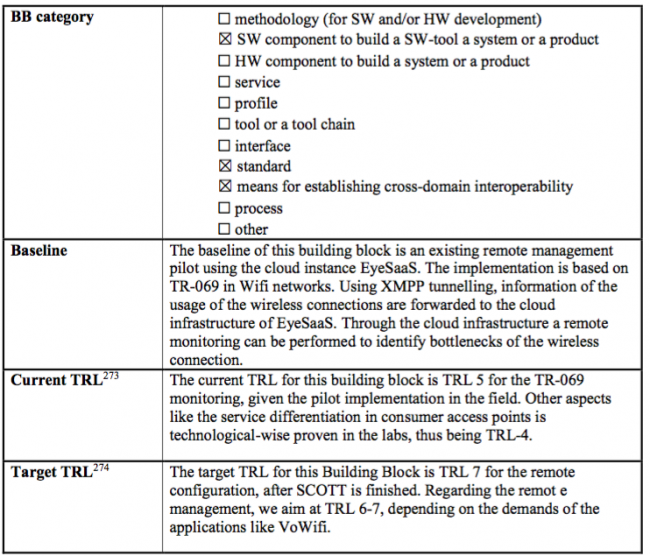
Remote Configuration of Infrastructure
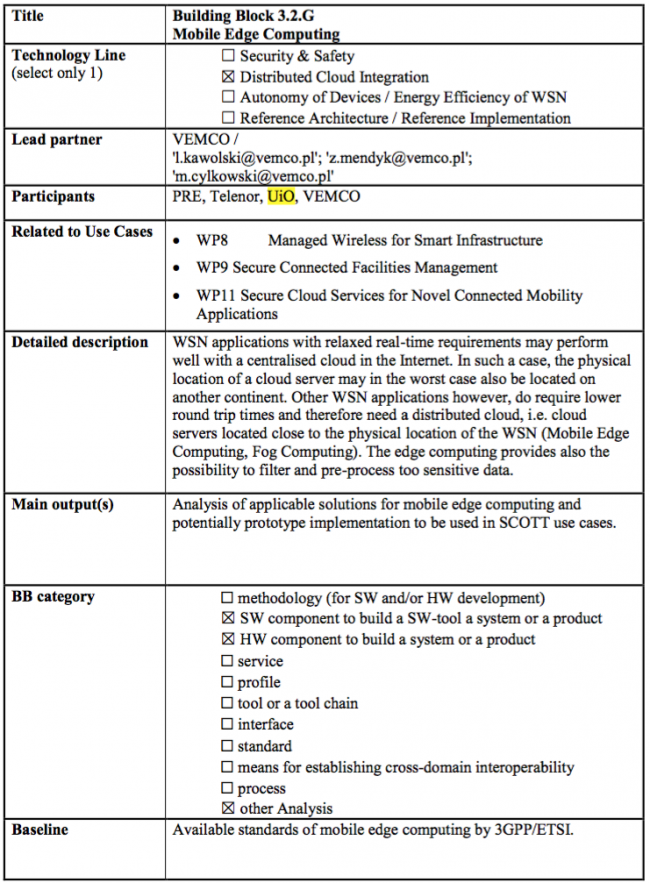
Mobile Edge Computing
Multi-metrics assessment for measurable security and privacy