Difference between revisions of "Overview of Responsibilities for UiO"
From its-wiki.no
(→SCOTT Security Core – Identification, authentication and secure communication) |
(→SCOTT Security Core – Identification, authentication and secure communication) |
||
| Line 29: | Line 29: | ||
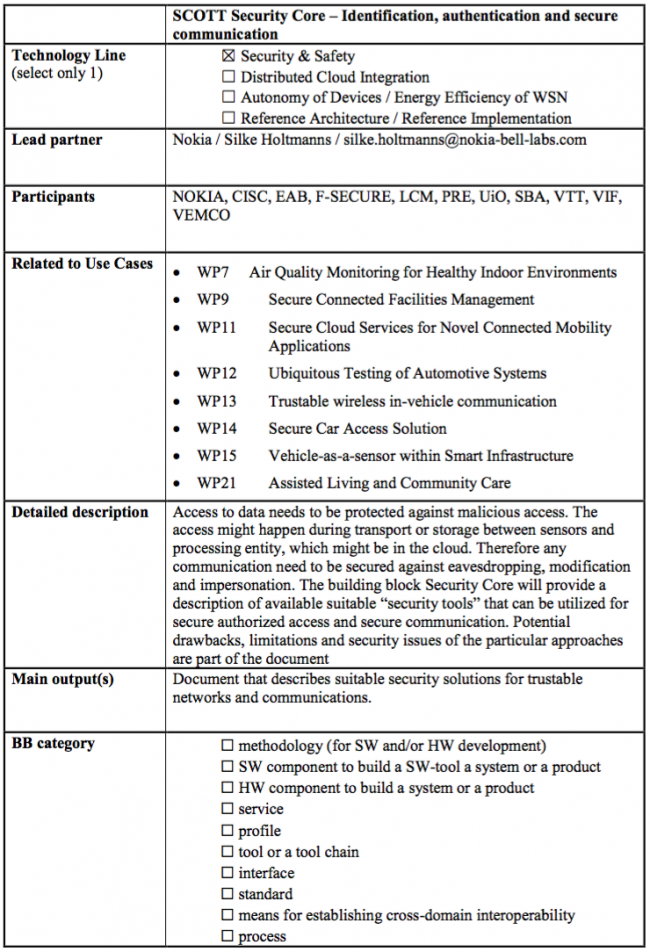
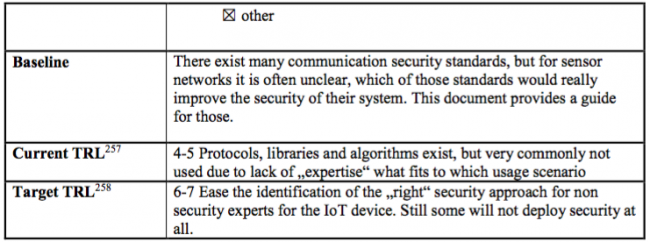
==SCOTT Security Core – Identification, authentication and secure communication== | ==SCOTT Security Core – Identification, authentication and secure communication== | ||
| − | [[File:SCOTT-NO_SCOTT Security Core – Identification, authentication and secure communication.png| | + | [[File:SCOTT-NO_SCOTT Security Core – Identification, authentication and secure communication.png|450px|SCOTT-WP30-Norway contribution]] |
[[File:SCOTT-NO_SCOTT Security Core – Identification, authentication and secure communication-p2.png|650px|SCOTT-WP30-Norway contribution]] | [[File:SCOTT-NO_SCOTT Security Core – Identification, authentication and secure communication-p2.png|650px|SCOTT-WP30-Norway contribution]] | ||
[[File:SCOTT-NO_SCOTT Security Core – Identification, authentication and secure communication-p3.png|650px|SCOTT-WP30-Norway contribution]] | [[File:SCOTT-NO_SCOTT Security Core – Identification, authentication and secure communication-p3.png|650px|SCOTT-WP30-Norway contribution]] | ||
Revision as of 13:35, 2 June 2017
| Wiki for ITS | ||||||
|---|---|---|---|---|---|---|
|
Contents
- 1 UiO Main tasks within the project
- 2 UiO involvement in Work Packages
- 3 UiO Related Building Blocks
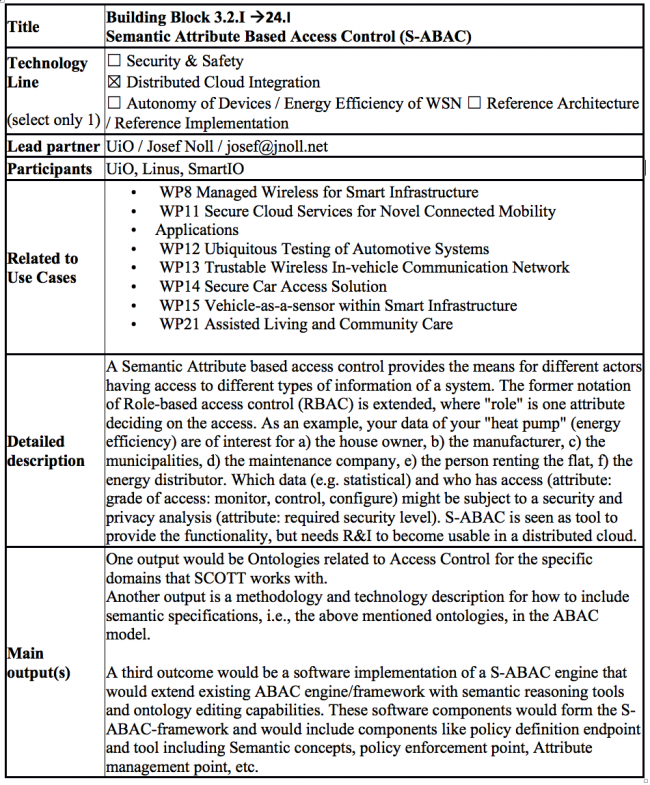
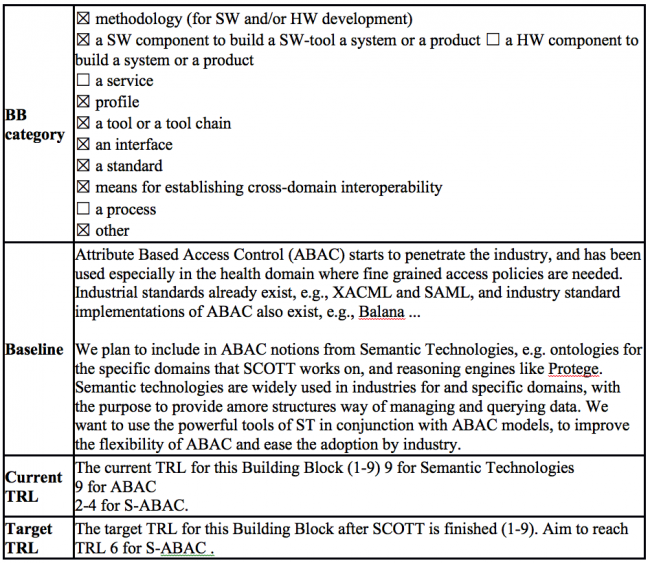
- 3.1 Semantic Attribute Based Access Control (S-ABAC)
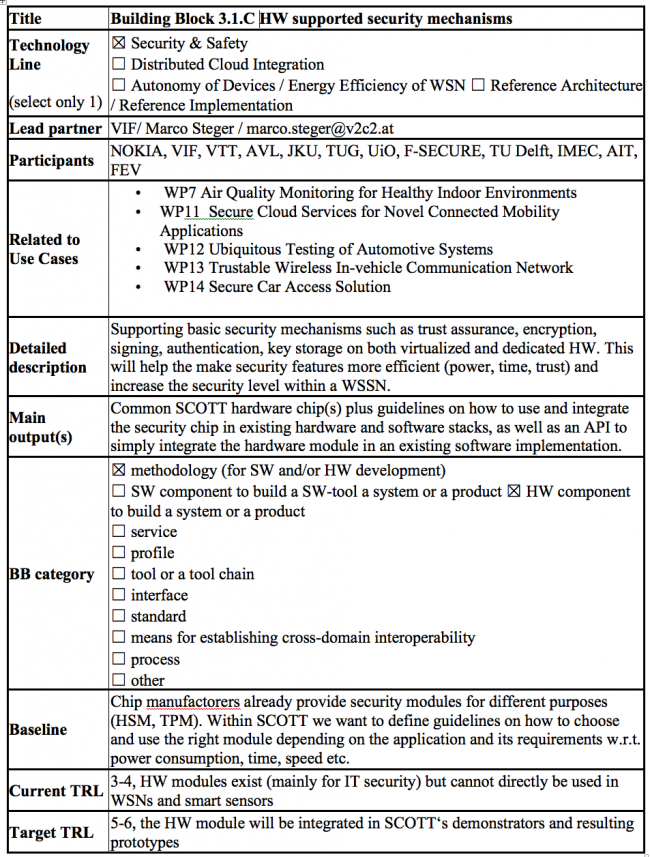
- 3.2 HW supported security mechanisms
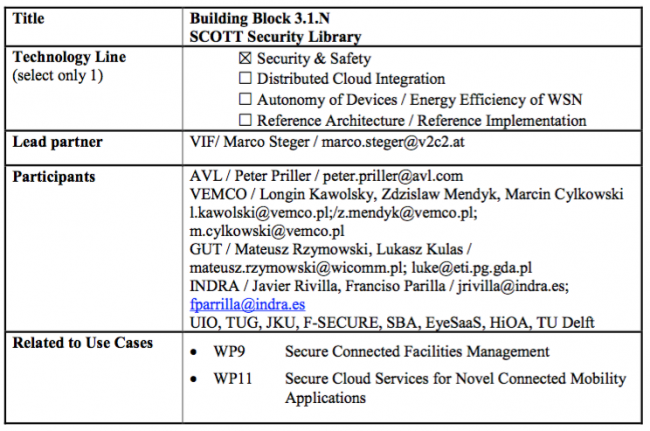
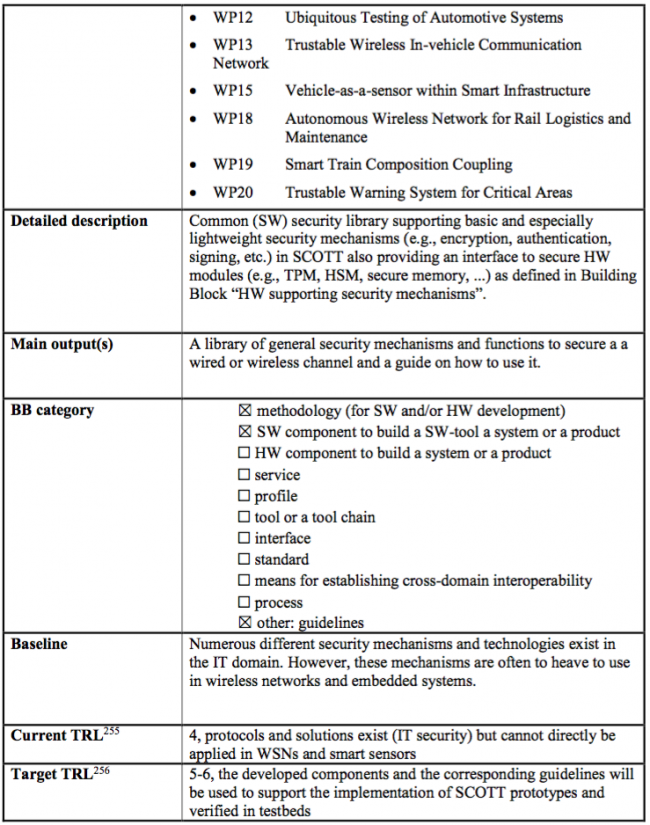
- 3.3 SCOTT Security Library
- 3.4 SCOTT Security Core – Identification, authentication and secure communication
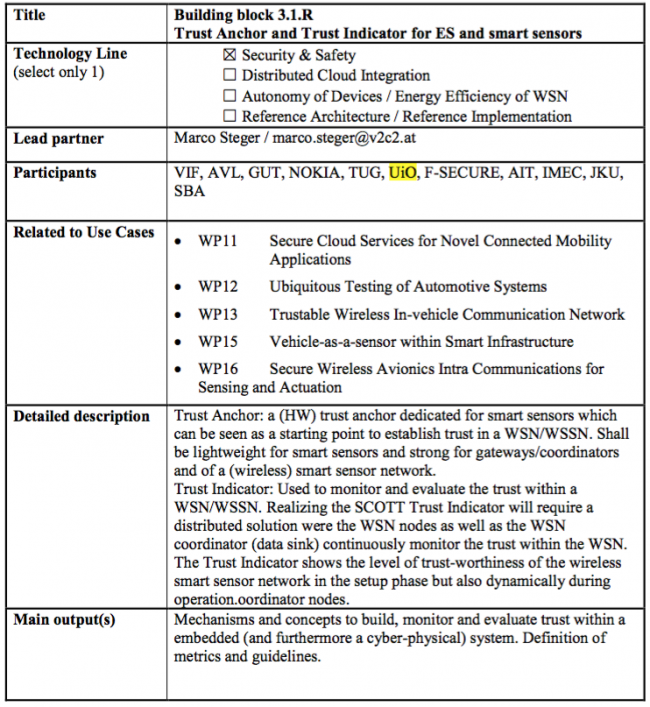
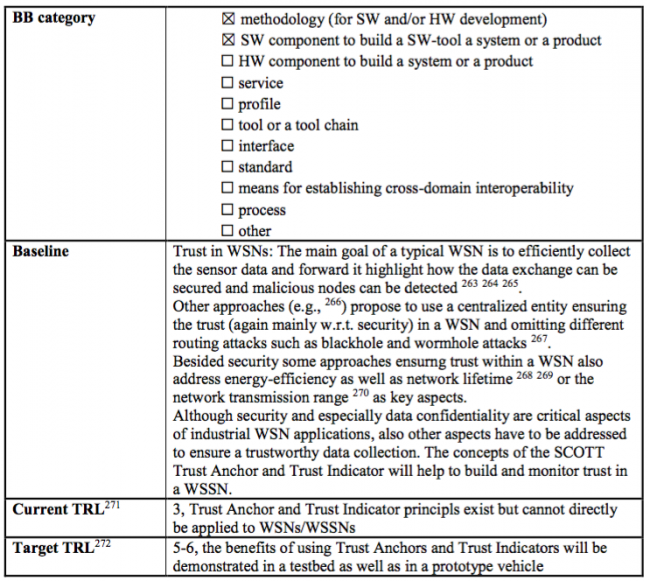
- 3.5 Trust Anchor and Trust Indicator for ES and smart sensors
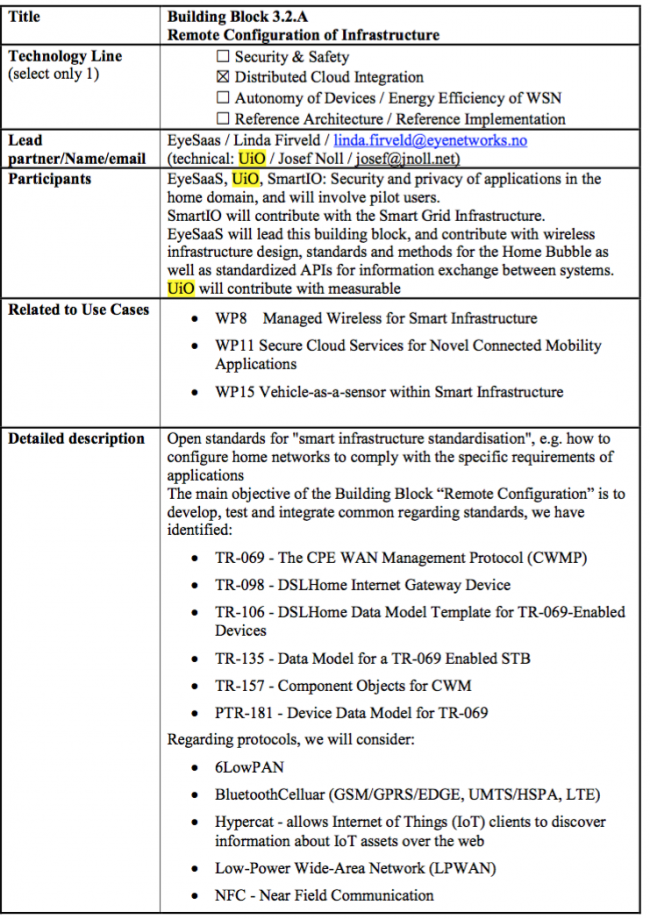
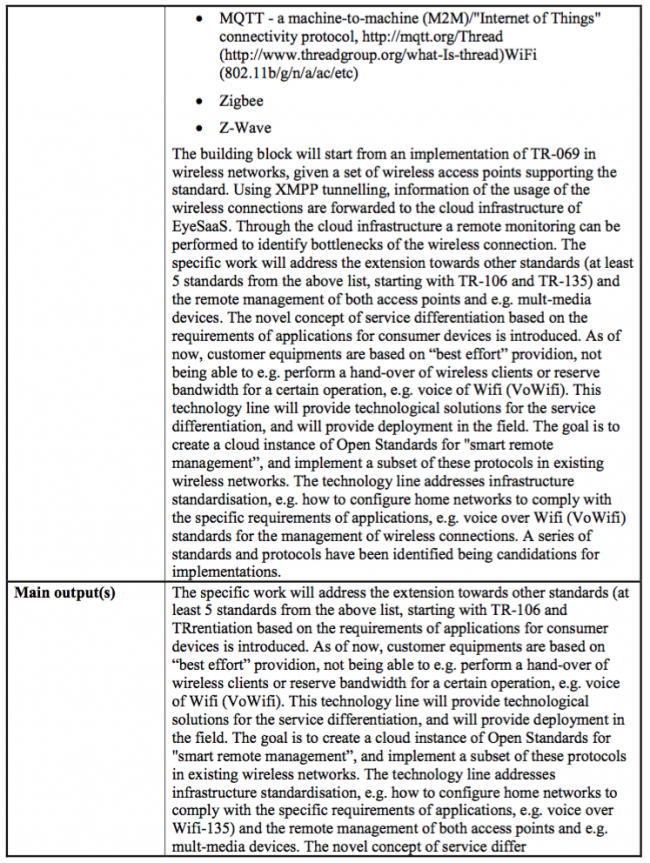
- 3.6 Remote Configuration of Infrastructure
- 3.7 Mobile Edge Computing
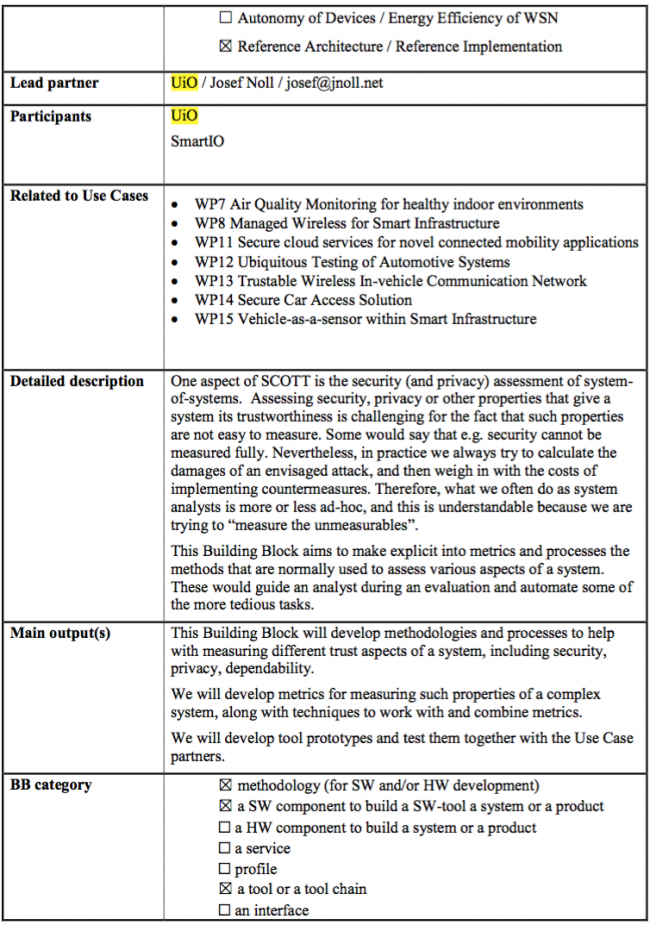
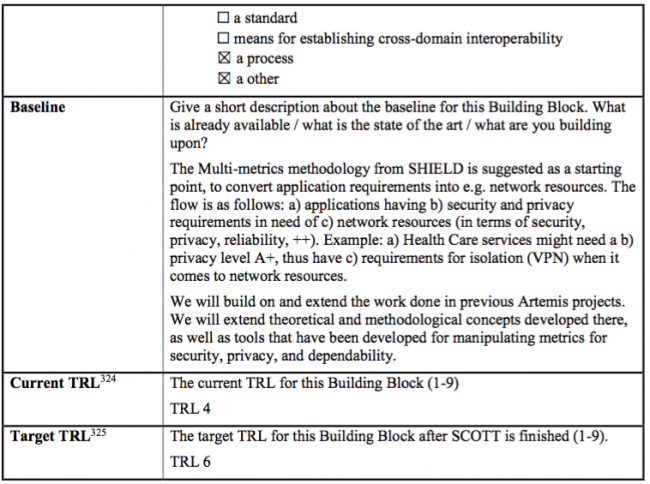
- 3.8 Multi-metrics assessment for measurable security and privacy
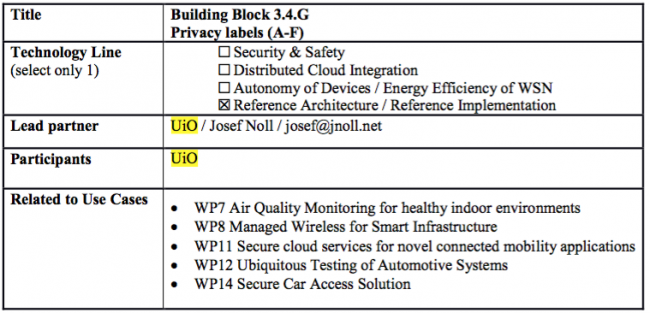
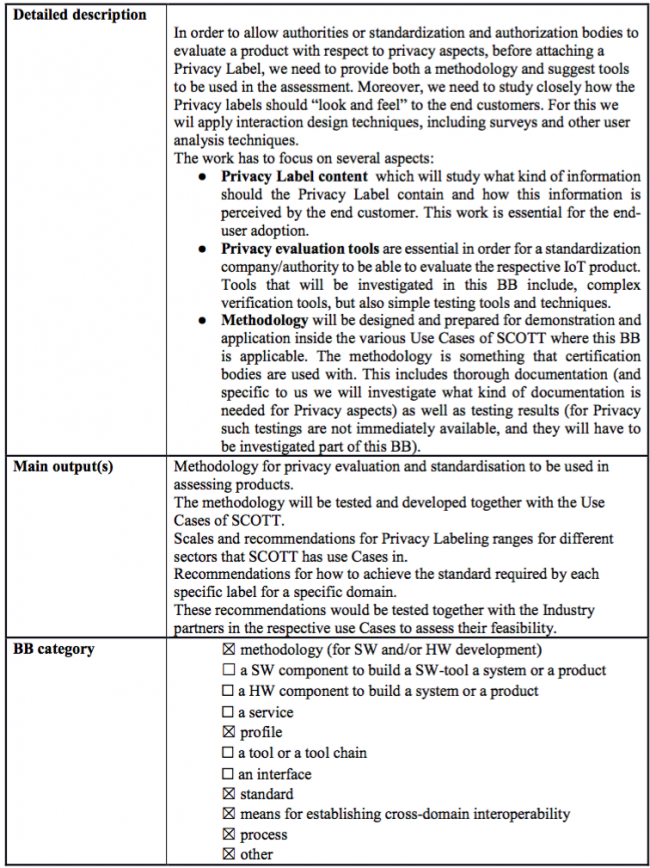
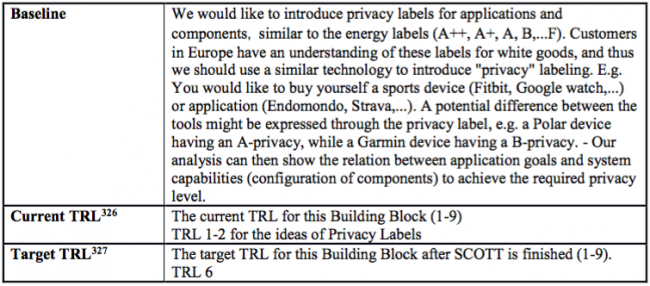
- 3.9 Privacy labels (A-F)
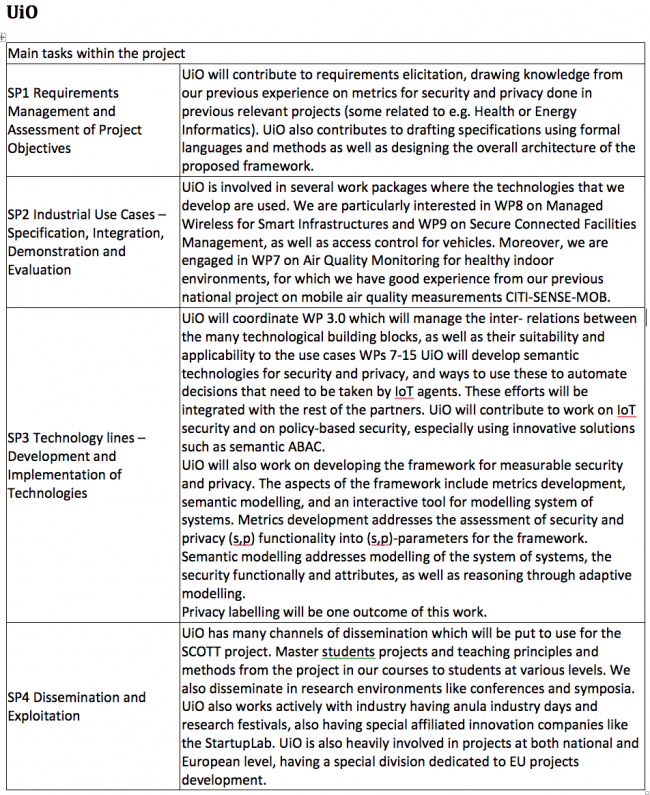
UiO Main tasks within the project
WT6 Summary of project effort in person-months for UiO
UiO involvement in Work Packages
Overview of UiO involvement in Work Packages in details
UiO Related Building Blocks
Semantic Attribute Based Access Control (S-ABAC)
HW supported security mechanisms
SCOTT Security Library
SCOTT Security Core – Identification, authentication and secure communication
Trust Anchor and Trust Indicator for ES and smart sensors
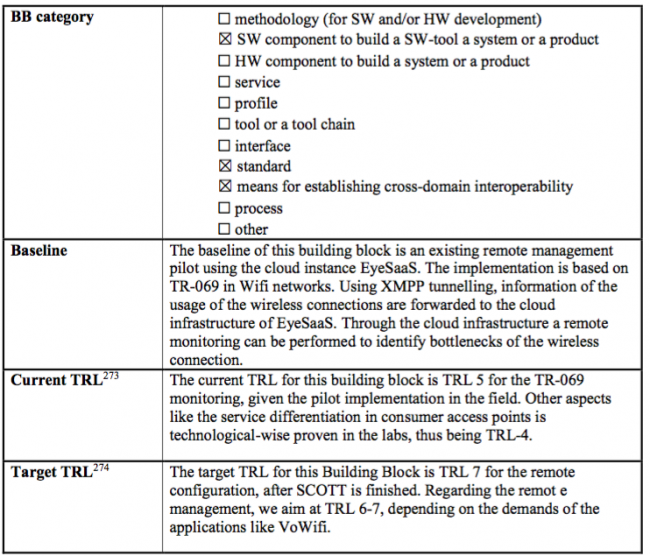
Remote Configuration of Infrastructure
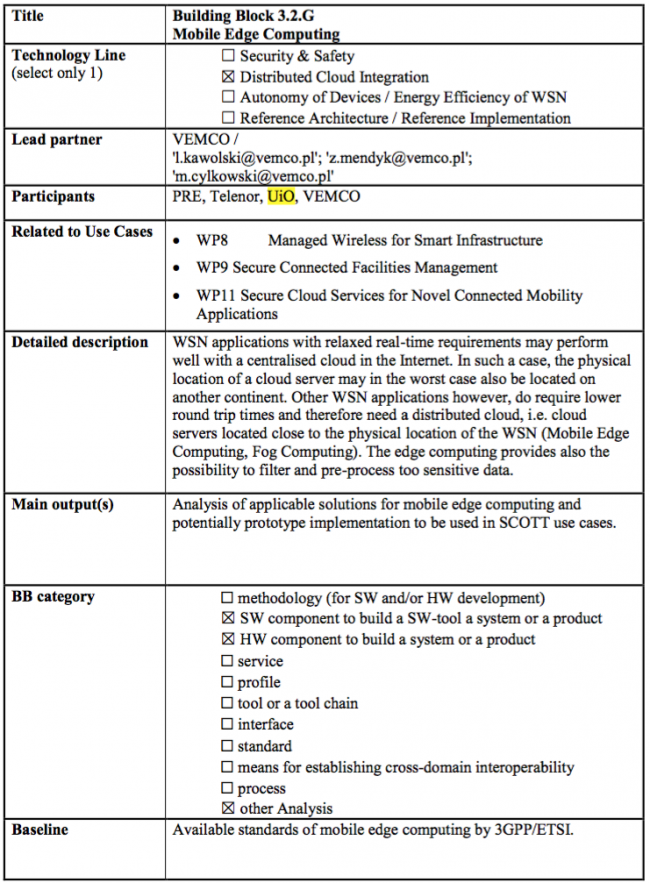
Mobile Edge Computing
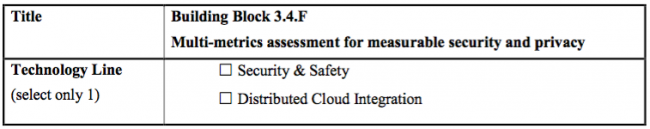
Multi-metrics assessment for measurable security and privacy