Difference between revisions of "TEK5500"
Josef.Noll (Talk | contribs) (→Lecture plan 2013) |
Josef.Noll (Talk | contribs) |
||
| Line 17: | Line 17: | ||
=Lectures overview= | =Lectures overview= | ||
| − | {{#ask: [[Category:UNIK4250]][[Date::> | + | {{#ask: [[Category:UNIK4250]][[Date::>2014]] |
| ?Date | | ?Date | ||
| sort=Date | | sort=Date | ||
| Line 24: | Line 24: | ||
}} | }} | ||
To add new lectures, use: [[Special:FormEdit/Lecture|Add a lecture]] | To add new lectures, use: [[Special:FormEdit/Lecture|Add a lecture]] | ||
| + | |||
= Course content = | = Course content = | ||
| Line 35: | Line 36: | ||
| − | = Earlier | + | = Earlier lectures= |
| − | {{#ask: [[Category:UNIK4250]][[Date::< | + | {{#ask: [[Category:UNIK4250]][[Date::<2013]] |
| ?Date | | ?Date | ||
| sort=Date | | sort=Date | ||
Revision as of 07:47, 10 March 2014
| Wiki for ITS | ||||||
|---|---|---|---|---|---|---|
|
TEK5500 - Security in Distributed Systems
| TEK5500 | |
|---|---|
| News | main info is on fronter, only selected lectures are here on the wiki |
| Organisation | UNIK |
| by | Nils Nordbotten, Josef Noll, Leif Nilsen |
| Keywords |
|---|
| Abstract | Encryption and key distributions in mobile and wireless networks on all layers |
|---|---|
| Objective (max 350 words) | learn about security principles, applied for systems |
| Keywords | Encryption, cryptography, authentication, authorization, key distribution, security, mobile security, wireless security, IPsec, DNSSEC, Firewall, Cyber Security |
| Research Area(s) | Security |
| Type of course | Master |
Upload TEK5500.png to see a course picture instead of the banner picture. Edit the page by Special:FormEdit/Course/TEK5500.
To add new lectures, use: Add a lecture
Course content
The course tackles the concept of security and gives a short introduction into cryptography. The threats to distributed computer systems are mentioned, as are the basic mechanisms that are used to make computer systems secure, plus the more complex mechanisms. There will also be some mention of making databases secure, as these are exposed to some extra threats, above and beyond the usual.
Lecture plan
Lecture plan is on Fronter
| DateThis property is a special property in this wiki. | |
|---|---|
| Mobile network security | 17 April 2015 |
To add new lectures, use: Add a lecture
The course tackles the concept of security and gives a short introduction into cryptography. The threats to distributed computer systems are mentioned, as are the basic mechanisms that are used to make computer systems secure, plus the more complex mechanisms. There will also be some mention of making databases secure, as these are exposed to some extra threats, above and beyond the usual.
Learning outcomes
The course presents threats to distributed computer systems, with the main emphasis being on threats that can be countered with software and hardware solutions. The course aims to communicate an understanding of the problems involved in the security of distributed systems, based on the principles of computer system security.
Specific Lecture Information
The handouts will be published on fronter
| DateThis property is a special property in this wiki. | |
|---|---|
| Mobile network security S11 | 13 January 2011 |
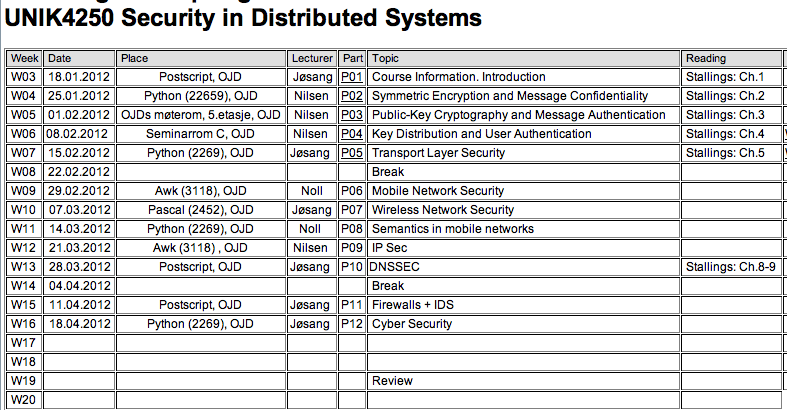
Course overview 2012
- UNIK4250:Slides_v2012 - info fra 2012